Contact Us
Error: Contact form not found.
Contact Us
Error: Contact form not found.
Client Login
Select a platform below to log in

NIST developed version 2.0 of the Cybersecurity Framework (CSF) to address increased cybersecurity threats and preparedness needs.

Is cloud storage enough to keep a business up and running when disaster strikes? See what you can do to protect your network from trouble.

XZ Utils, a popular data compression software, was significantly compromised when it contained malicious code, posing a risk of unauthorized system access.

Understand the key elements of a SOC 2 report and how to interpret them effectively to evaluate vendor reliability.

As we enter 2024, we must prioritize cybersecurity initiatives and integrate them into our business strategies.

Two zero-day vulnerabilities have recently been uncovered in the widely used Ivanti VPN devices, which are actively being exploited.

A recent cyberattack affected hospitals in multiple states, diverting ambulances from emergency rooms in Texas, Oklahoma, New Jersey, and New Mexico.

With Microsoft 365 becoming a mainstream platform, be sure to read this comprehensive guide to strengthening your environment.

Implementing a patch management policy in information security has become a necessity rather than an option. There are key things to remember.
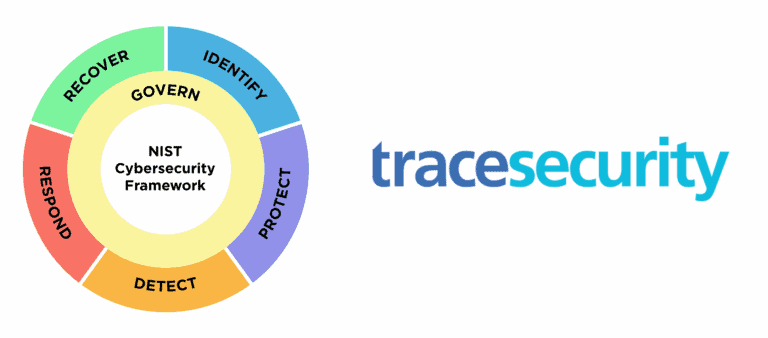
The National Institute of Standards and Technology (NIST) has made significant improvements with the release of the CSF 2.0 draft.