Contact Us
[contact-form-7 id="ceb4db8" title="Contact form 1"]
Contact Us
[contact-form-7 id="ceb4db8" title="Contact form 1"]
Client Login
Select a platform below to log in


The National Credit Union Association released the 2026 Supervisory Priorities for Credit Unions. The ISE Program is still going strong.

Many organizations have taken to taking advantage of a vCISO, or virtual Chief Information Security Officer.
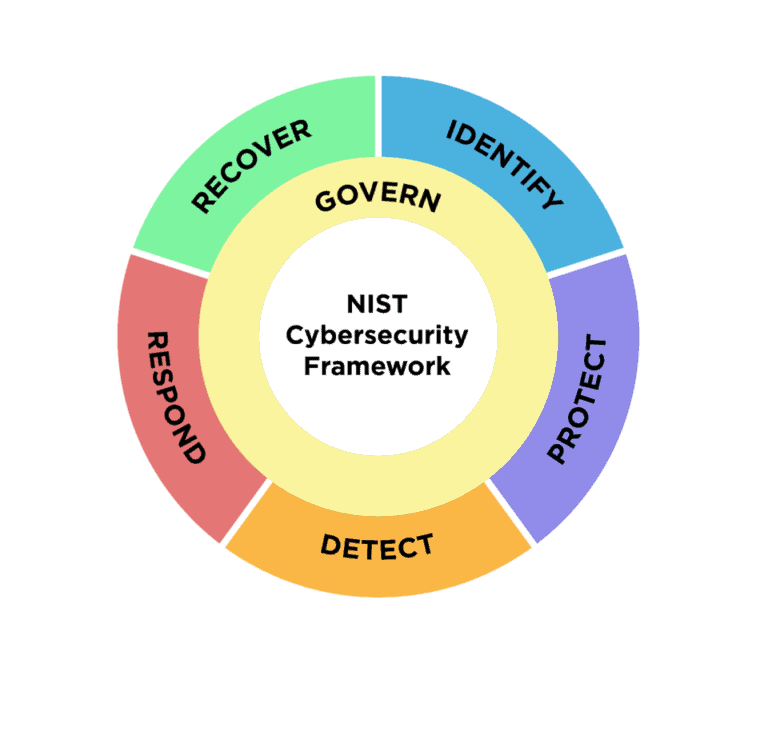
TraceSecurity's Cybersecurity Assessment Tool has been updated to NIST 2.0

Impersonations are a big part of phishing. After gathering information, bad actors will try to appear as someone they're not.

While not a common form of social engineering, USB drops can still cause a lot of problems. Never use a USB drive off the ground.

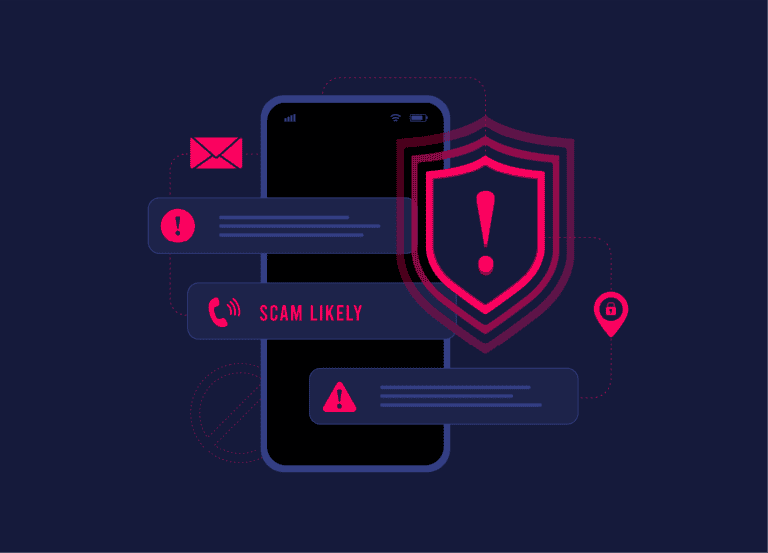
Text messages have become a common form of social engineering. Be sure to keep an eye out for unknown numbers.
Vishing has become a more common form of social engineering. It is cause for concern when people can replicate your voice.

Learn about how attackers are targeting users through email.
Attackers use a variety of social engineering attacks to breach your organization