Contact Us
[contact-form-7 id="ceb4db8" title="Contact form 1"]
Contact Us
[contact-form-7 id="ceb4db8" title="Contact form 1"]
Client Login
Select a platform below to log in

Introduction In today’s digital world, the protection of sensitive and personally identifiable information (PII) is crucial, especially for financial institutions such as banks and credit unions. We trust these organizations with mass amounts of private data, making them prime attack…

Back in May of 2021, the Colonial Pipeline was attacked with ransomware that shut down the entire operation for multiple days. This led to millions in losses.

Schools and universities are being targeted by cyber attacks like never before. Be sure that your defenses are up to par.

There is a difference between IT and OT when it comes to technology and how businesses use it. It usually comes down to the type of equipment being used.

Identify the differences between Incident Response and others, the usefulness of them, and what NIST and FFIEC regulations have to say about them.
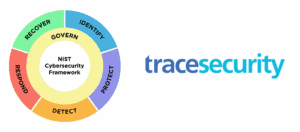
The National Institute of Standards and Technology (NIST) has made significant improvements with the release of the CSF 2.0 draft.