Contact Us
[contact-form-7 id="ceb4db8" title="Contact form 1"]
Contact Us
[contact-form-7 id="ceb4db8" title="Contact form 1"]
Client Login
Select a platform below to log in
Cybersecurity compliance can be confusing for many organizations, but it doesn’t have to be. There are many resources for government regulations.

With the constantly changing environment of technology, it’s important to keep systems up to date with a vulnerability scanner like Qualys.

A recent cyberattack affected hospitals in multiple states, diverting ambulances from emergency rooms in Texas, Oklahoma, New Jersey, and New Mexico.

The NCUA made a mid-year update to incident reporting requirements.

There is a difference between IT and OT when it comes to technology and how businesses use it. It usually comes down to the type of equipment being used.
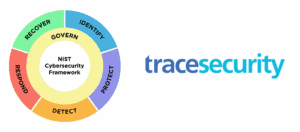
The National Institute of Standards and Technology (NIST) has made significant improvements with the release of the CSF 2.0 draft.

Following the Colonial Pipeline ransomware attack, the TSA has implemented cybersecurity regulations for pipeline owners and operators.