Contact Us
[contact-form-7 id="ceb4db8" title="Contact form 1"]
Contact Us
[contact-form-7 id="ceb4db8" title="Contact form 1"]
Client Login
Select a platform below to log in

Learn more about the CIS Critical Security Controls and how to use them to better secure your business.
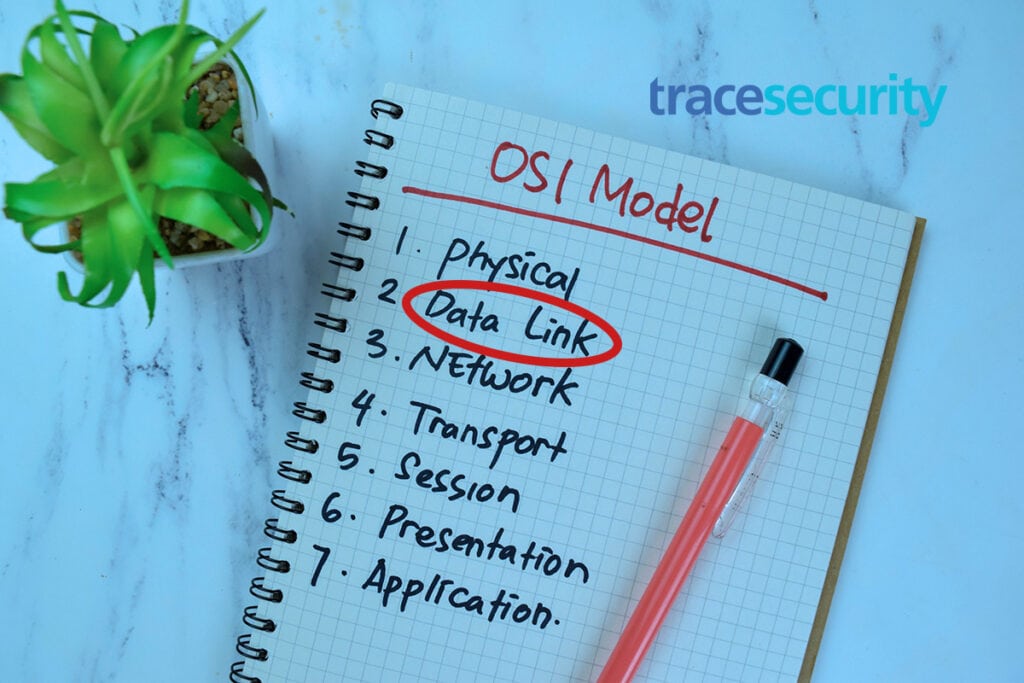
The Open Systems Interconnection (OSI) model is a conceptual framework. Learn how to secure the data link layer

What is Ethical Hacking? Ethical hacking is one of the most important resources companies can invest in to protect their data amidst the growing frequency of attacks on their security. Ethical hacking involves authorizing hackers to attempt to gain unauthorized…

The Open Systems Interconnection (OSI) model is a conceptual framework. Learn how to secure the physical layer.
The Basics of Phishing Phishing uses the art of deception to get users to divulge sensitive information. An attacker will send emails that seem to be from a legitimate source, like a shipping reminder or bank notification, but is actually…

Protect your websites and apps from cybersecurity attacks with web application security testing.