Contact Us
[contact-form-7 id="ceb4db8" title="Contact form 1"]
Contact Us
[contact-form-7 id="ceb4db8" title="Contact form 1"]
Client Login
Select a platform below to log in

Steganography can be anything from hiding passwords inside of images to creating passwords out of ordinary objects.

The Farm Credit Administration (FCA) announced a new cyber risk management rule effective January 1, 2025.

NIST developed version 2.0 of the Cybersecurity Framework (CSF) to address increased cybersecurity threats and preparedness needs.

The holidays are times of enjoyment, but also present additional attack avenues for hackers.

The Open Systems Interconnection (OSI) model is a conceptual framework. This is how you secure the application layer.
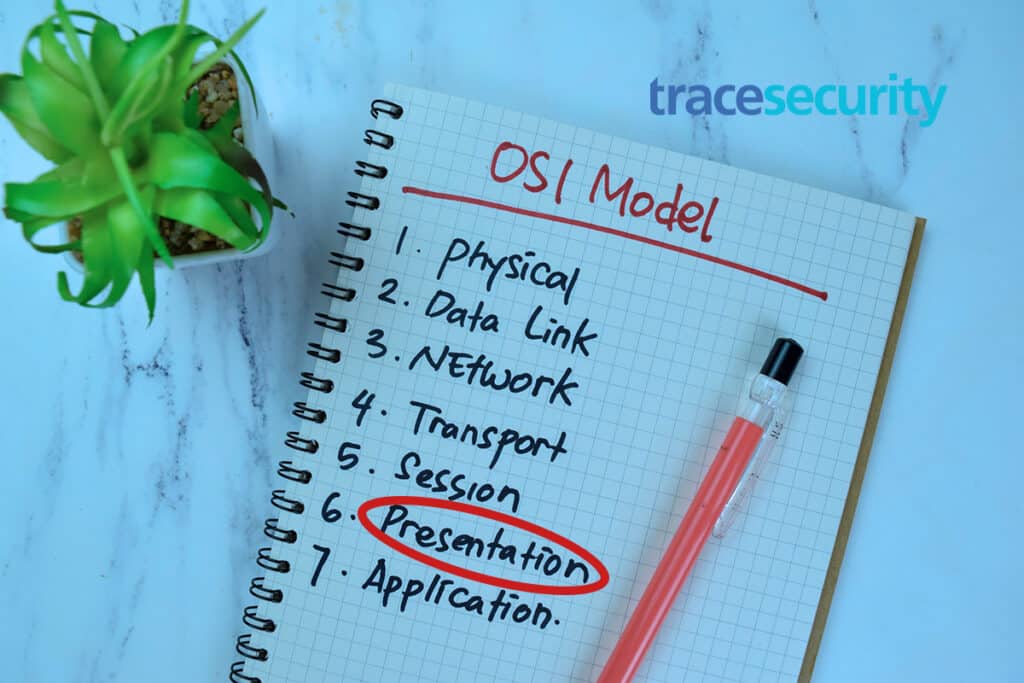
The Open Systems Interconnection (OSI) model is a conceptual framework. Learn how to secure the presentation layer.