Contact Us
[contact-form-7 id="ceb4db8" title="Contact form 1"]
Contact Us
[contact-form-7 id="ceb4db8" title="Contact form 1"]
Client Login
Select a platform below to log in

There is a difference between IT and OT when it comes to technology and how businesses use it. It usually comes down to the type of equipment being used.

Watch the webinar on how attackers continue to breach organizations through remote social engineering.

Identify the differences between Incident Response and others, the usefulness of them, and what NIST and FFIEC regulations have to say about them.
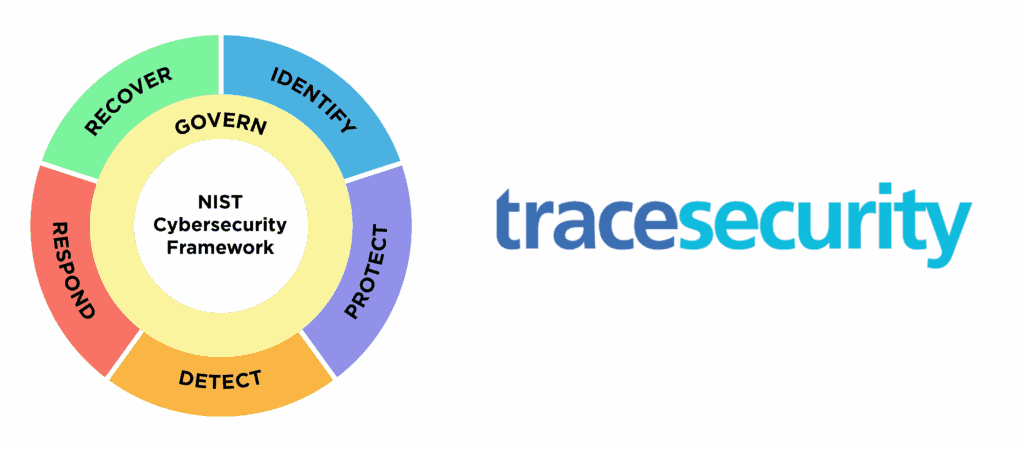
The National Institute of Standards and Technology (NIST) has made significant improvements with the release of the CSF 2.0 draft.

Many large enterprises implement SIEM solutions, however, smaller institutions are hesitant when it comes to investing in these programs.

The Volt Typhoon cyberattack was a strategically planned campaign that targeted foundational sectors of the US. This is how it happened.