Introduction
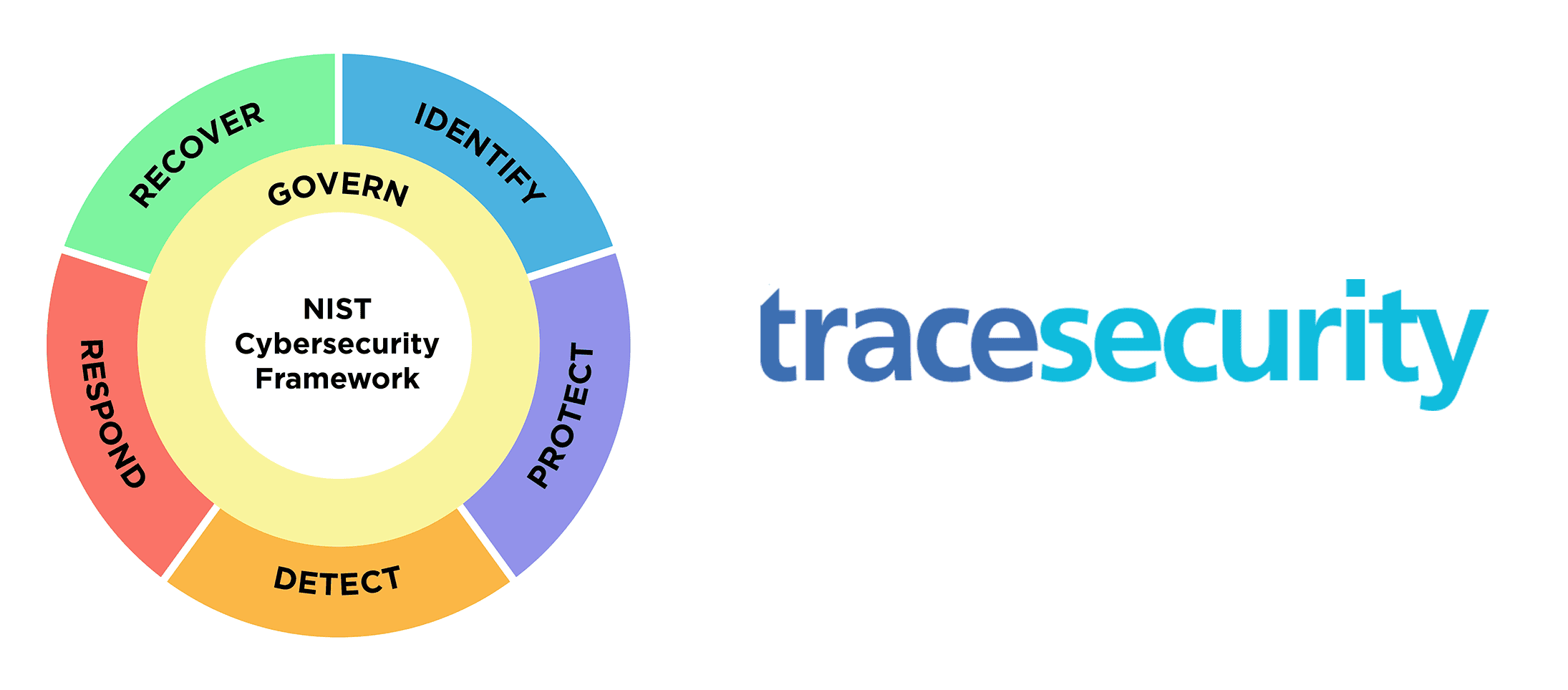
The National Institute of Standards and Technology (NIST) has made significant improvements with the release of the CSF 2.0 draft, providing more clarity on control expectations. In addition to this updated framework is the GOVERN (GV) pillar. This pillar ensures that organizations establish, oversee, and continuously monitor their cybersecurity risk management strategies, expectations, and policies.
Shortcomings of NIST CSF 1.1
While NIST CSF 1.1 has been lauded for its robust guidelines and flexible approach toward establishing cybersecurity frameworks, it wasn’t without its limitations:
- Generic Guidelines – One of the primary critiques was its generic nature. While it was designed to cater to a broad range of industries, it often lacked specificity for certain sectors, leaving organizations to grapple with how best to apply some of its guidelines.
- Evolution of Threat Landscape – With the ever-changing dynamics of cyber threats, some critics felt that CSF 1.1 didn’t evolve quickly enough to address newer cyber-attack forms, leaving entities potentially exposed to unforeseen risks.
- Lack of Emphasis on Organizational Context – While CSF 1.1 promoted best practices, it didn’t always emphasize the importance of tailoring strategies based on individual organizations’ unique contexts and nuances. This often led to a one-size-fits-all approach, which may not have been optimal for all entities.
- Limited Coverage of Supply Chain Risks – Modern businesses operate within intricate supply chains, and a vulnerability in any part can compromise the whole. CSF 1.1 was critiqued for not providing a comprehensive approach to managing these supply chain risks.
- Ambiguity in Metrics and Measurement – While CSF 1.1 advocated for measuring cybersecurity efficacy, it didn’t always provide clear metrics or methodologies for organizations to gauge their success or areas of improvement.
- Overemphasis on Technology, Underemphasis on Culture – Cybersecurity isn’t just about technological solutions; it’s also about fostering a culture of security awareness. Some critics believed CSF 1.1 leaned too heavily on the former, with insufficient guidelines on building and nurturing a security-aware culture.
While NIST CSF 1.1 provided a solid foundation, these shortcomings highlighted the need for revisions, leading to the development and introduction of the improved and more comprehensive CSF 2.0.
Breaking Down the “Govern” Pillar
Before diving into the “Govern” Pillar, we want to emphasize that it is still in the draft phase, so specific controls might change. As such, we are reviewing each section’s general control expectations. The “Govern” pillar lays the foundation for an organization’s cybersecurity infrastructure. It emphasizes establishing, communicating, and overseeing roles, responsibilities, and policies that ensure a proactive and adaptive approach to cybersecurity.
- Organizational Context (GV.OC) – This section underscores the importance of tailoring cybersecurity strategies and actions according to the organization’s specific context. A one-size-fits-all approach might not address unique vulnerabilities or capitalize on specific strengths. Organizations can devise effective strategies by understanding their operational environment, mission, objectives, stakeholders, and processes.
- Roles, Responsibilities, and Authorities (GV.RR) – Clear definition of roles ensures no overlaps or gaps in cybersecurity functions. It emphasizes leadership’s accountability and the integration of cybersecurity considerations across all hierarchical levels, from top-level executives to operational staff. The goal is to create a coherent, unified approach where everyone knows their part and responsibilities.
- Policies, Processes, and Procedures (GV.PO) – Beyond defining roles, it’s crucial to outline the policies, processes, and procedures that guide cybersecurity implementation and maintenance. This involves establishing clear guidelines and ensuring they are communicated throughout the organization. But, as cybersecurity threats evolve, these policies need periodic reviews and updates to remain effective.
- Oversight (GV.OV) – This section emphasizes the importance of continually evaluating the cybersecurity infrastructure’s effectiveness. It’s not enough to set policies in motion; there must be mechanisms to measure how well they work and where improvements can be made. It advocates for a reflective approach, constantly asking whether the current strategies align with organizational objectives and the prevailing threat landscape.
The “Govern” pillar provides a blueprint for organizations to anchor their cybersecurity efforts, ensuring they’re systematic, comprehensive, and adaptable. It promotes an integrated approach where cybersecurity is seen not as a standalone function but intertwined with organizational strategy, culture, and operations.
Conclusion
The release of CSF 2.0 in 2024, with the introduction of the GOVERN pillar, represents a much-needed advancement in cybersecurity risk management. This refined approach emphasizes clarity in objectives, risk definition, and weaving cybersecurity into overarching risk management. By adopting the GOVERN pillar, organizations can adeptly traverse today’s intricate cybersecurity environment, transforming threats into avenues for resilience and growth. As digital threats evolve, the NIST CSF 2.0 offers timely tools and insights to fortify organizational futures.
References
Discussion Draft: The NIST Cybersecurity Framework 2.0 Core with Implementation Examples
https://www.nist.gov/document/discussion-draft-nist-cybersecurity-framework-20-core-implementation-examples
Public Draft: The NIST Cybersecurity Framework 2.0 National Institute of Standards and Technology
https://nvlpubs.nist.gov/nistp…